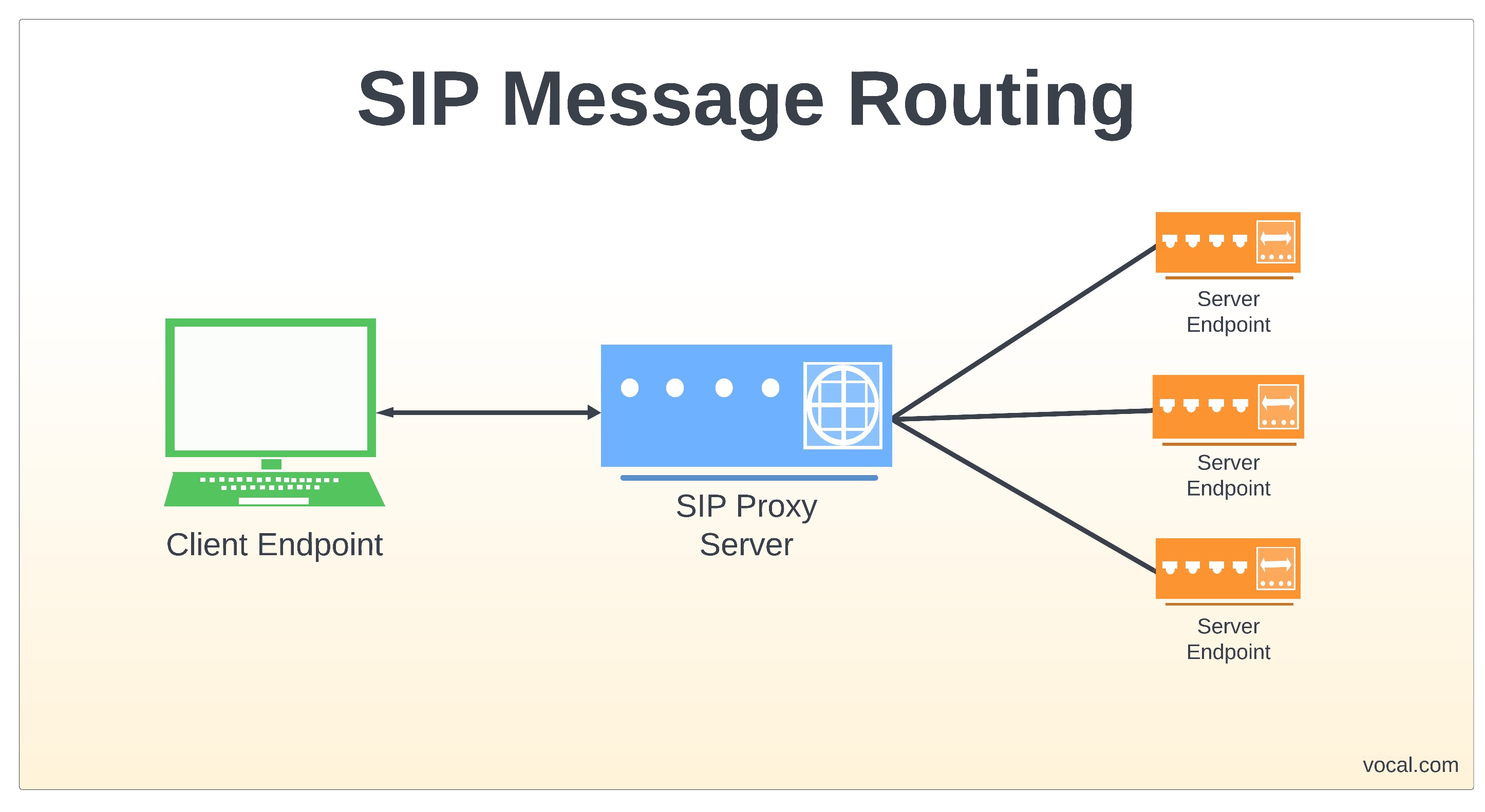
SIP Message Routing can be accomplished using different protocols including UDP, TCP, SCTP, and TLS depending on user messaging requirements for reliability and security. SIP can also adapt different routing to accommodate network congestion and latency to meet these requirements.
UDP
SIP request and response messages are sent individually in a single datagram. For large messages, field names can be specified with a single character such as “v” for “Via” to reduce the number of characters and fit within the maximum packet size. If messages are too large, they must be sent using TCP since SIP is unable to handle fragmented messages at the application layer. Since UDP is not reliable, lost messages will result in additional messages being transmitted which could further aggravate an already congested network that may have caused the messages to be lost in the first place. Other than message checksum errors, UDP does not have a means to detect lost messages and depends on higher layer applications to perform this check using:
- Retransmission timers
- Increasing command sequences numbers
- Positive acknowledgements
TCP
SIP message transmissions using TCP require a connection be established between the two endpoints. Messages are sent with a response timeout to determine when a message is lost. Whenever a client sends a SIP message, the TCP server responds back with an acknowledge message to which the client then responds with another acknowledge or data message. This three way handshake is reliable but also adds complexity and delays to a SIP message transfer. In addition, servers must maintain state information at the transport layer.
SCTP
Although SCTP message transfers are similar to TCP, it has several advantages over TCP. SCTP supports message segmentation at the transport layer and unlike TCP, when a segment is lost SCTP avoids head-of-the-line blocking of other message segments during retransmission. It continues to send messages to the application layer while requesting retransmission of the message. SCTP also supports multi-homing such that when a server fails, messages can be received at another without the additional overhead to switch.
TLS
SIP messages sent using TLS are encrypted to protect data from third party interception. TLS has two distinct layers – Handshake and Transport. The Handshake layer establishes the connection, negotiates encryption, and provides authentication. One time certificates are exchanged during the handshake to use for authentication. The Transport layer provides for reliable and private transport of the encrypted data. Although TLS has security advantages of over UDP and TCP, data encryption imposes additional overhead during message transfers which can increase latency. When two proxies use TLS, mutual authentication may be done with certificates or with SIP digest. For multiple hops, S/MIME must be used to ensure end-to-end encryption.
VOCAL’s software libraries provide a range of solutions using UDP, TCP, SCTP, and TLS protocols for SIP message routing to meet reliability and security requirements for a variety of applications and platforms.
Features
- SIP messages can be routed using UDP, TCP, SCTP or TLS protocols
- SIP supports end-to-end and hop-by-hop authentication, as well as end-to-end encryption using S/MIME
SIP Software
VOCAL’s embedded libraries include a complete range of ETSI / ITU / IEEE compliant algorithms, in addition to many other standard and proprietary algorithms. Our SIP source code is optimized for execution on ANSI C and leading DSP architectures from TI, ADI, AMD, Intel, ARM, MIPS, and other vendors. The SIP software libraries are modular and can be executed as a single task under a variety of operating systems or standalone with its own microkernel.
More Information
- VoIP Software
- VoIP Design
- WebRTC
- RFC 3261 Standard
- SIP Analog Modem Server (SAMS)
- The Transport Layer Security (TLS) Protocol Version 1.3
- SIP Software Modules
- SIP Conferencing
- SIP Presence and Instant Messaging
- SIP Registration
- SIP User Authentication
- Secure SIP
- Session Initiation Protocol (SIP) and Deep Packet Inspection (DPI)
- SIP Trunking
VOCAL Technologies has been in business for over 30 years and is an engineering design house that can provide a custom solution that meets your unique communication requirements.
Please contact us to discuss your communication application requirements.