Steganography is the art of hiding sensitive data in media, whether it be text, image, video, or more recently, network. When secrecy is a must, encryption of data (when used properly), will almost always keep that data away from prying eyes, but while encryption hides the payload, it does nothing to hide the fact that there IS sensitive data being transmitted. Steganography is the answer to that problem. Steganography hides the fact that a message was ever sent and when used with encryption, provides secure transmission while being obscure to any snooping.
Steganography in VoIP
Steganography has a home in VOIP and network communication as well. In a more traditional sense, steganography has been used to hide data in images by manipulating the least significant bits, or audio by adding and/or removing hard to hear frequencies. When Steganography is used in a VOIP setting there are many ways to hide data.
One such way is to insert false packets during negotiation or realtime connection (network steganography). By purposefully adding incorrectly formatted packets, the sender has a means of communicating with a peer. The receiving VOIP application will drop these false packets, replacing them using packet loss concealment or prediction algorithms. The receiving party, privy to the knowledge of steganography, can then use these dropped packets to formulate the message. Throughout this secret transmission, the VOIP application continues to function normally, giving no indication of a message sent.
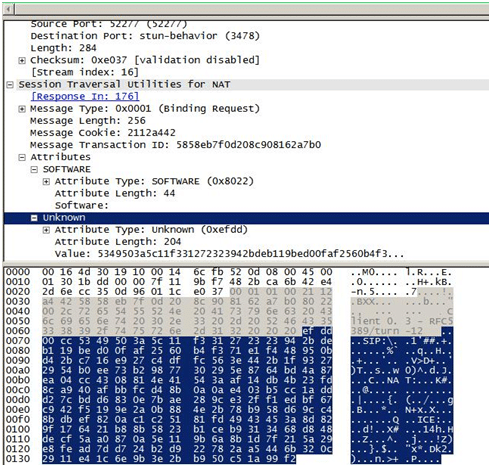
Another technique is to conceal data within SIP/RTP header fields that will be ignored or are unused. If a VOIP connection has been established using RTP as transport, an unused RTCP field can be hijacked to disguise information. This added info will be ignored by the receiving VOIP application, but is available to anybody that knows to look there.
In addition to packet based steganography, one can also use the properties of VOIP communication to come up with other ways of concealment. Echo cancellation is a process utilised by almost every VOIP application. By modifying the echo cancellation routine, one can insert sensitive data into conversation without disturbing the natural flow. Echo cancellation routines are not perfect and are often implemented differently. Only someone knowing to look for a message in the return echo would ever know of the concealed transmission.
There are many other viable methods of using steganography within a VOIP context. All it really takes is an idea and the participants knowledge of where to look for the information.