VOCAL’s Session Initiation Protocol (SIP) Software Library implements
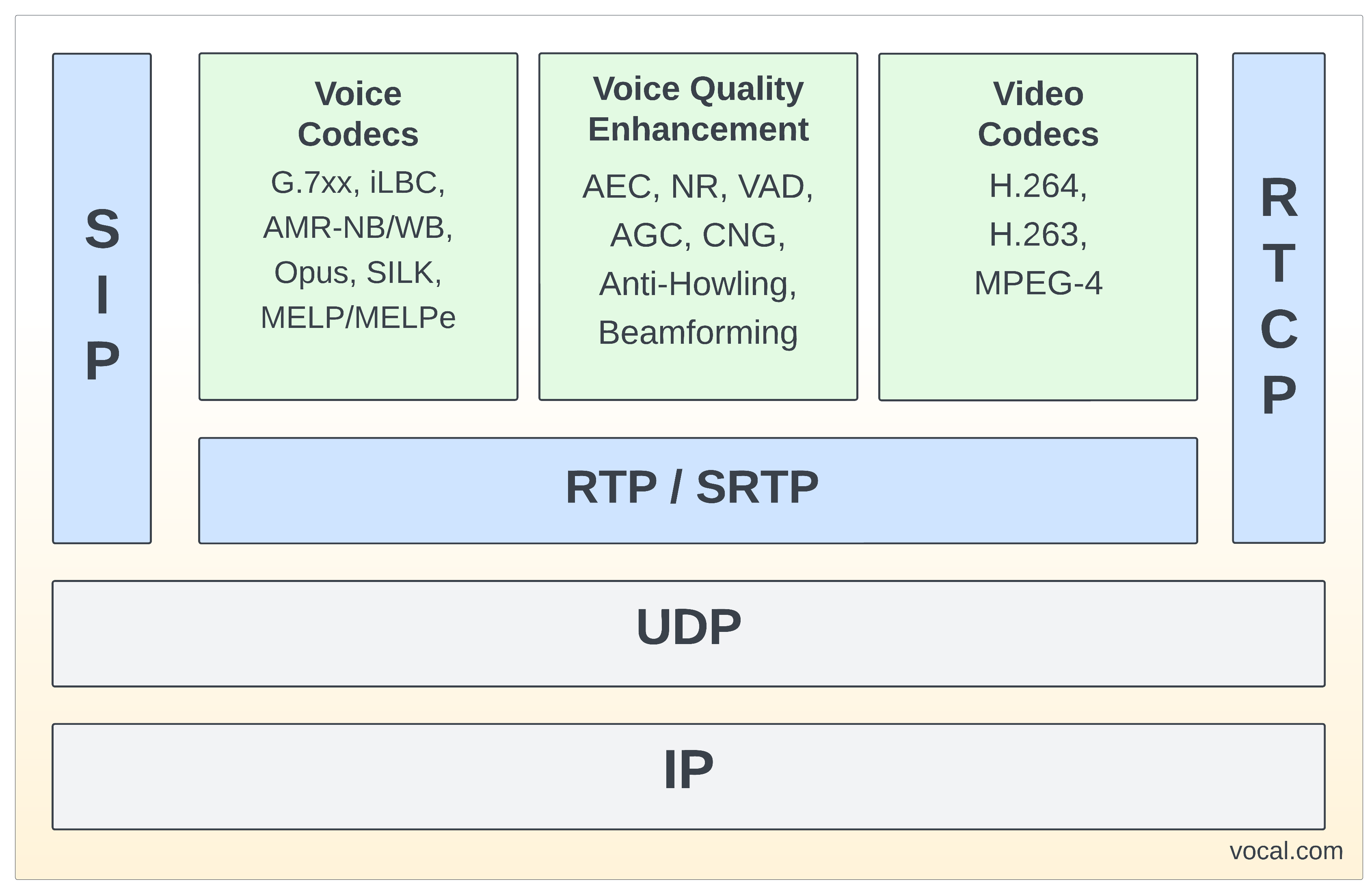
RFC 3261 with full support for SIP client and server applications. Our cross platform SIP stack can be combined with our comprehensive software library of algorithms and protocols to implement VoIP, mobile (VoNR, VoLTE, Dialer), voice and video conferencing, Radio over IP (RoIP), Modem and Fax over IP, Serial over IP and multimedia applications. Contact us to discuss your specific SIP application requirements. Custom designs are also available.
VOCAL’s server, cloud and embedded libraries include a complete range of ETSI / ITU / IEEE compliant algorithms, in addition to many other standard and proprietary algorithms. Our SIP software is optimized for execution on all major general purpose and DSP architectures (Intel, AMD, ARM, Texas Instruments (TI), Analog Devices (ADI), MIPS, etc.) and portable enough to run on just about anything. The software libraries are modular and can be executed as a single task under a variety of operating systems or standalone with its own microkernel or our small network stack.
Session Initiation Protocol
Session Initiation Protocol is an application-layer control protocol that can establish, modify, and terminate multimedia sessions (conferences) such as Internet telephony calls using Voice over IP (VoIP). SIP supports user applications that require the creation and management of a session, where a session is considered an exchange of data between an association of participants. The implementation of these applications is complicated by the practices of participants: users may move between endpoints, they may be addressable by multiple names, and they may communicate in several different media – sometimes simultaneously.
Session Initiation Protocol can invite participants to already existing sessions, such as multicast conferences. Numerous protocols have been authored that carry various forms of real-time multimedia session data such as voice, video, or text messages. SIP works in concert with these protocols by enabling Internet endpoints (called user agents) to discover one another and to agree on a characterization of a session they would like to share. Media can be added to (and removed from) an existing session.
Session Initiation Protocol transparently supports name mapping and redirection services for enhanced personal mobility. To locate prospective session participants, and other functions, SIP enables the creation of an infrastructure of network hosts (called proxy servers) to which user agents can send registrations, invitations to sessions, and other requests. It is an agile, general-purpose tool for creating, modifying, and terminating sessions that works independently of underlying transport protocols and without dependency on the type of session that is being established.
Session Initiation Protocol supports:
- User location: determination of the end system to be used for communication
- User availability: determination of the called party to engage in communications
- User capabilities: determination of the media and media parameters to be used
- Session setup: “ringing”, establishment of session parameters at both called and calling party
- Session management: transfer and terminate sessions, modify session parameters, and invoke services
Session Initiation Protocol provides a suite of security services, which include denial-of-service prevention, authentication (both user to user and proxy to user), integrity protection, and encryption and privacy services.
SIP is used in conjunction with other protocols to provide complete services to the end user including:
- RTP and RTCP for transporting real-time data and providing QoS feedback
- RTSP for controlling delivery of streaming media
- MEGACO or MGCP for controlling gateways to the PSTN
- SDP for describing multimedia sessions.
- Eurocae ED-137 uses SIP and RTP for Air Traffic Control and other RoIP applications
- AS-SIP – part of the Department of Defense (DOD) Unified Capabilities (UC) Requirements (UCR) for end-end to end assured services
- SIPconnect 2.0 is an umbrella specification to ensure reliable interconnect between SIP endpoints and networks – (Future versions considered as a possible replacement for AS-SIP
SIP Protocol Library Features
- Compliant with RFC 3261 SIP v.2
- Supports both IPv4 and IPv6
- Support SIPS/TLS
- Supports SDP Offer/Answer
- Supports Conferencing
- ED137 support available
- Support for Audio, Video, Serial, Radio and more
- Supports end-to-end and hop-by-hop authentication and end-to-end encryption using S/MIME.
- MISRA compliant version (with limited deviations) available
- Assured Services (AS) Session Initiation Protocol (SIP) 2013 (AS-SIP 2013) features available, including support for RFC4412 Communications Resource Priority for the Session Initiation Protocol (SIP)
- RFC6442 Location Conveyance for the Session Initiation Protocol support available
Applications
- Voice over IP
- Embedded Devices
- Cloud Communications
- Modem over IP Solutions
- Fax over IP Solutions
- IOT / M2M
- Wideband IP telephony
- Audio and Video Conferencing and MCUs
- WebRTC Telecom Interfacing
- UAV to Ground Communications
- Manned Spacecraft
- IP Intercom
- WIFI phones VoWLAN
- GPRS/EDGE/VoLTE systems
- Personal Communication Devices
SIP Pages
- SIP Software Modules
- SIP Analog Modem Server (SAMS)
- SIP Call Forwarding
- SIP Conferencing
- SIP Message Routing
- SIP Presence
- SIP Registration
- SIP User Authentication
- Secure SIP
- Session Initiation Protocol (SIP) and Deep Packet Inspection (DPI)
- SIP Trunking
- SIP Agents
- SIP Servers
VOCAL’s solution is available for the above platforms. Please contact us for specific supported platforms.

